The evolution of computing has at all times concerned vital technological developments. The most recent developments are a large leap into quantum computing period. Early computer systems, just like the ENIAC, had been massive and relied on vacuum tubes for fundamental calculations. The invention of transistors and built-in circuits within the mid-Twentieth century led to smaller, extra environment friendly computer systems. The event of microprocessors within the Nineteen Seventies enabled the creation of non-public computer systems, making expertise accessible to the general public.
Over the many years, steady innovation exponentially elevated computing energy. Now, quantum computer systems are of their infancy. That is utilizing quantum mechanics ideas to handle advanced issues past classical computer systems’ capabilities. This development marks a dramatic leap in computational energy and innovation.
Quantum Computing Fundamentals and Affect
Quantum computing originated within the early Nineteen Eighties, launched by Richard Feynman, who advised that quantum techniques may very well be extra effectively simulated by quantum computer systems than classical ones. David Deutsch later formalized this concept, proposing a theoretical mannequin for quantum computer systems.
Quantum computing leverages quantum mechanics to course of info in a different way than classical computing. It makes use of qubits, which might exist in a state 0, 1 or each concurrently. This functionality, generally known as superposition, permits for parallel processing of huge quantities of data. Moreover, entanglement permits qubits to be interconnected, enhancing processing energy and communication, even throughout distances. Quantum interference is used to control qubit states, permitting quantum algorithms to resolve issues extra effectively than classical computer systems. This functionality has the potential to rework fields like cryptography, optimization, drug discovery, and AI by fixing issues past classical pc’s attain.
Safety and Cryptography Evolution
Threats to safety and privateness have advanced alongside technological developments. Initially, threats had been less complicated, reminiscent of bodily theft or fundamental codebreaking. As expertise superior, so did the sophistication of threats, together with cyberattacks, knowledge breaches, and id theft. To fight these, sturdy safety measures had been developed, together with superior cybersecurity protocols and cryptographic algorithms.
Cryptography is the science of securing communication and knowledge by encrypting it into codes that require a secret key for decryption. Classical cryptographic algorithms are two most important sorts – symmetric and uneven. Symmetric, exemplified by AES, makes use of the identical key for each encryption and decryption, making it environment friendly for big knowledge volumes. Uneven key cryptography, together with RSA and ECC for authentication, entails public-private key pair, with ECC providing effectivity via smaller keys. Moreover hash features like SHA guarantee knowledge integrity and Diffie-Hellman for key exchanges strategies which allow safe key sharing over public channels. Cryptography is important for securing web communications, defending databases, enabling digital signatures, and securing cryptocurrency transactions, taking part in a significant function in safeguarding delicate info within the digital world.
Public key cryptography is based on mathematical issues which might be simple to carry out however troublesome to reverse, reminiscent of multiplying massive primes. RSA makes use of prime factorization, and Diffie-Hellman depends on the discrete logarithm downside. These issues type the safety foundation for these cryptographic techniques as a result of they’re computationally difficult to resolve shortly with classical computer systems.
Quantum Threats
Probably the most regarding facet of the transition to a quantum computing period is the potential menace it poses to present cryptographic techniques.
Encryption breaches can have catastrophic outcomes. This vulnerability dangers exposing delicate info and compromising cybersecurity globally. The problem lies in creating and implementing quantum-resistant cryptographic algorithms, generally known as post-quantum cryptography (PQC), to guard towards these threats earlier than quantum computer systems turn into sufficiently highly effective. Guaranteeing a well timed and efficient transition to PQC is vital to sustaining the integrity and confidentiality of digital techniques.
Comparability – PQC, QC and CC
Publish-quantum cryptography (PQC) and quantum cryptography (QC) are distinct ideas.
Beneath desk illustrates the important thing variations and roles of PQC, Quantum Cryptography, and Classical Cryptography, highlighting their goals, methods, and operational contexts.
| Function | Publish-Quantum Cryptography (PQC) | Quantum Cryptography (QC) | Classical Cryptography (CC) |
|---|---|---|---|
| Goal | Safe towards quantum pc assaults | Use quantum mechanics for cryptographic duties | Safe utilizing mathematically arduous issues |
| Operation | Runs on classical computer systems | Entails quantum computer systems or communication strategies | Runs on classical computer systems |
| Strategies | Lattice-based, hash-based, code-based, and so on. | Quantum Key Distribution (QKD), quantum protocols | RSA, ECC, AES, DES, and so on. |
| Function | Future-proof present cryptography | Leverage quantum mechanics for enhanced safety | Safe knowledge primarily based on present computational limits |
| Focus | Shield present techniques from future quantum threats | Obtain new ranges of safety utilizing quantum ideas | Present safe communication and knowledge safety |
| Implementation | Integrates with present communication protocols | Requires quantum applied sciences for implementation | Broadly carried out in present techniques and networks |
Insights into Publish-Quantum Cryptography (PQC)
The Nationwide Institute of Requirements and Expertise (NIST) is at the moment reviewing a wide range of quantum-resistant algorithms:
| Cryptographic Sort | Key Algorithms | Foundation of Safety | Strengths | Challenges |
|---|---|---|---|---|
| Lattice-Primarily based | CRYSTALS-Kyber, CRYSTALS-Dilithium |
Studying With Errors (LWE), Shortest Vector Downside (SVP) | Environment friendly, versatile; robust candidates for standardization | Complexity in understanding and implementation |
| Code-Primarily based | Basic McEliece | Decoding linear codes | Sturdy safety, many years of study | Massive key sizes |
| Hash-Primarily based | XMSS, SPHINCS+ | Hash features | Easy, dependable | Requires cautious key administration |
| Multivariate Polynomial | Rainbow | Techniques of multivariate polynomial equations | Reveals promise | Massive key sizes, computational depth |
| Isogeny-Primarily based | SIKE (Supersingular Isogeny Key Encapsulation) | Discovering isogenies between elliptic curves | Compact key sizes | Issues about long-term safety because of cryptanalysis |
As summarized above, Quantum-resistant cryptography encompasses numerous approaches. Every provides distinctive strengths, reminiscent of effectivity and robustness, but additionally faces challenges like massive key sizes or computational calls for. NIST’s Publish-Quantum Cryptography Standardization Challenge is working to scrupulously consider and standardize these algorithms, making certain they’re safe, environment friendly, and interoperable.
Quantum-Prepared Hybrid Cryptography
Hybrid cryptography combines classical algorithms like X25519 (ECC-based algorithm) with post-quantum algorithms typically referred as “Hybrid Key Trade” to offer twin layer of safety towards each present and future threats. Even when one part is compromised, the opposite stays safe, making certain the integrity of communication.
In Might 2024, Google Chrome enabled ML-KEM (a post-quantum key encapsulation mechanism) by default for TLS 1.3 and QUIC enhancing safety for connections between Chrome Desktop and Google Companies towards future quantum pc threats.
Challenges
ML-KEM (Module Lattice Key Encapsulation Mechanism), which makes use of lattice-based cryptography, has bigger key shares because of its advanced mathematical constructions and wishes extra knowledge to make sure robust safety towards future quantum pc threats. The additional knowledge helps ensure the encryption is hard to interrupt, nevertheless it ends in larger key sizes in comparison with conventional strategies like X25519. Regardless of being bigger, these key shares are designed to maintain knowledge safe in a world with highly effective quantum computer systems.
Beneath desk offers a comparability of the important thing and ciphertext sizes when utilizing hybrid cryptography, illustrating the trade-offs by way of dimension and safety:
| Algorithm Sort | Algorithm | Public Key Dimension | Ciphertext Dimension | Utilization |
|---|---|---|---|---|
| Classical Cryptography | X25519 | 32 bytes | 32 bytes | Environment friendly key change in TLS. |
| Publish-Quantum Cryptography |
Kyber-512 | ~800 bytes | ~768 bytes | Average quantum-resistant key change. |
| Kyber-768 | 1,184 bytes | 1,088 bytes | Quantum-resistant key change. | |
| Kyber-1024 | 1,568 bytes | 1,568 bytes | Greater safety degree for key change. | |
| Hybrid Cryptography | X25519 + Kyber-512 | ~832 bytes | ~800 bytes | Combines classical and quantum safety. |
| X25519 + Kyber-768 | 1,216 bytes | 1,120 bytes | Enhanced safety with hybrid strategy. | |
| X25519 + Kyber-1024 | 1,600 bytes | 1,600 bytes | Sturdy safety with hybrid strategies. |
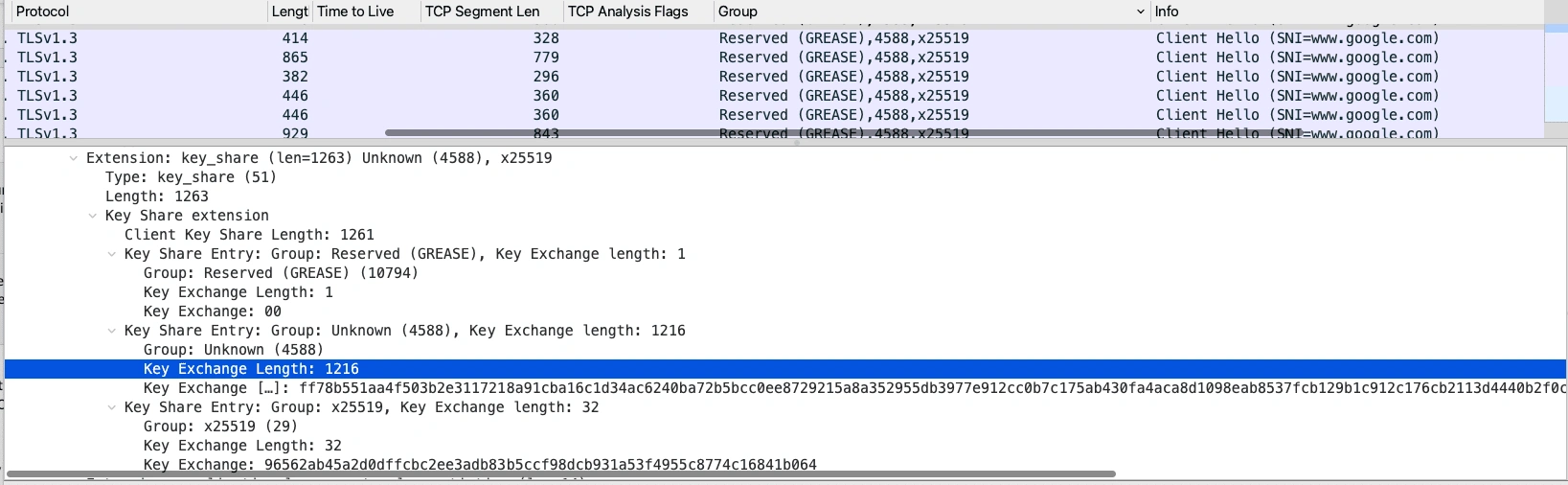
Within the following Wireshark seize from Google, the group identifier “4588” corresponds to the “X25519MLKEM768” cryptographic group inside the ClientHello message. This identifier signifies the usage of an ML-KEM or Kyber-786 key share, which has a dimension of 1216 bytes, considerably bigger than the standard X25519 key share dimension of 32 bytes:
As illustrated within the photos beneath, the combination of Kyber-768 into the TLS handshake considerably impacts the scale of each the ClientHello and ServerHello messages.
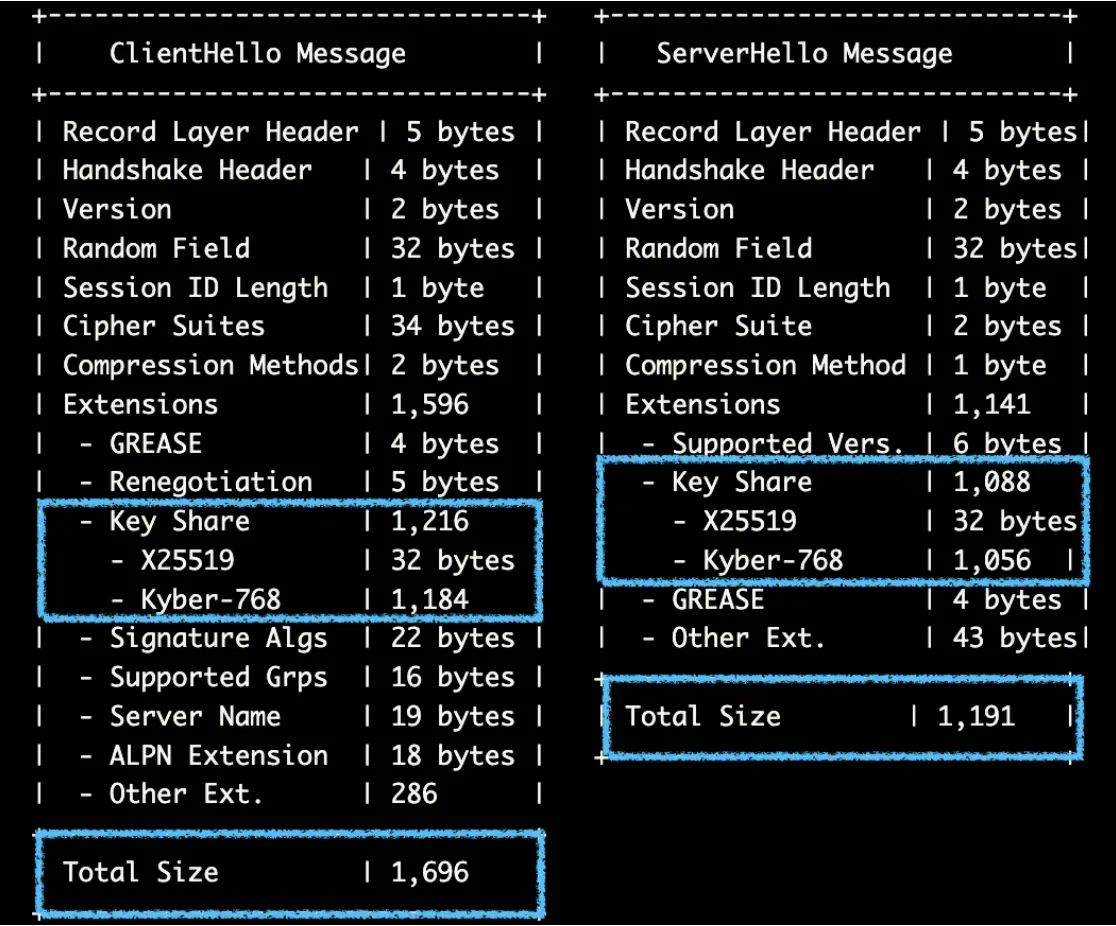
Future additions of post-quantum cryptography teams may additional exceed typical MTU sizes. Excessive MTU settings can result in challenges reminiscent of fragmentation, community incompatibility, elevated latency, error propagation, community congestion, and buffer overflows. These points necessitate cautious configuration to make sure balanced efficiency and reliability in community environments.
NGFW Adaptation
The combination of post-quantum cryptography (PQC) in protocols like TLS 1.3 and QUIC, as seen with Google’s implementation of ML-KEM, can have a number of implications for Subsequent-Era Firewalls (NGFWs):
- Encryption and Decryption Capabilities: NGFWs that carry out deep packet inspection might want to deal with the bigger TLS handshake messages because of ML-KEM bigger key sizes and ciphertexts related to PQC. This elevated knowledge load can require updates to processing capabilities and algorithms to effectively handle the elevated computational load.
- Packet Fragmentation: With bigger messages exceeding the everyday MTU, ensuing packet fragmentation can complicate visitors inspection and administration, as NGFWs should reassemble fragmented packets to successfully analyze and apply safety insurance policies.
- Efficiency Concerns: The adoption of PQC may impression the efficiency of NGFWs as a result of elevated computational necessities. This may necessitate {hardware} upgrades or optimizations within the firewall’s structure to take care of throughput and latency requirements.
- Safety Coverage Updates: NGFWs may want updates to their safety insurance policies and rule units to accommodate and successfully handle the brand new cryptographic algorithms and bigger message sizes related to ML-KEM.
- Compatibility and Updates: NGFW distributors might want to guarantee compatibility with PQC requirements, which can contain firmware or software program updates to help new cryptographic algorithms and protocols.
By integrating post-quantum cryptography (PQC), Subsequent-Era Firewalls (NGFWs) can present a forward-looking safety answer, making them extremely engaging to organizations aiming to guard their networks towards the constantly evolving menace panorama.
Conclusion
As quantum computing advances, it poses vital threats to present cryptographic techniques, making the adoption of post-quantum cryptography (PQC) important for knowledge safety. Implementations like Google’s ML-KEM in TLS 1.3 and QUIC are essential for enhancing safety but additionally current challenges reminiscent of elevated knowledge masses and packet fragmentation, impacting Subsequent-Era Firewalls (NGFWs). The important thing to navigating these adjustments lies in cryptographic agility—making certain techniques can seamlessly combine new algorithms. By embracing PQC and leveraging quantum developments, organizations can strengthen their digital infrastructures, making certain sturdy knowledge integrity and confidentiality. These proactive measures will prepared the ground in securing a resilient and future-ready digital panorama. As expertise evolves, our defenses should evolve too.
We’d love to listen to what you assume. Ask a Query, Remark Beneath, and Keep Linked with Cisco Safe on social!
Cisco Safety Social Channels
Share:

